Your Machines Make Parts.
SMC Makes the Workflow Defensible.
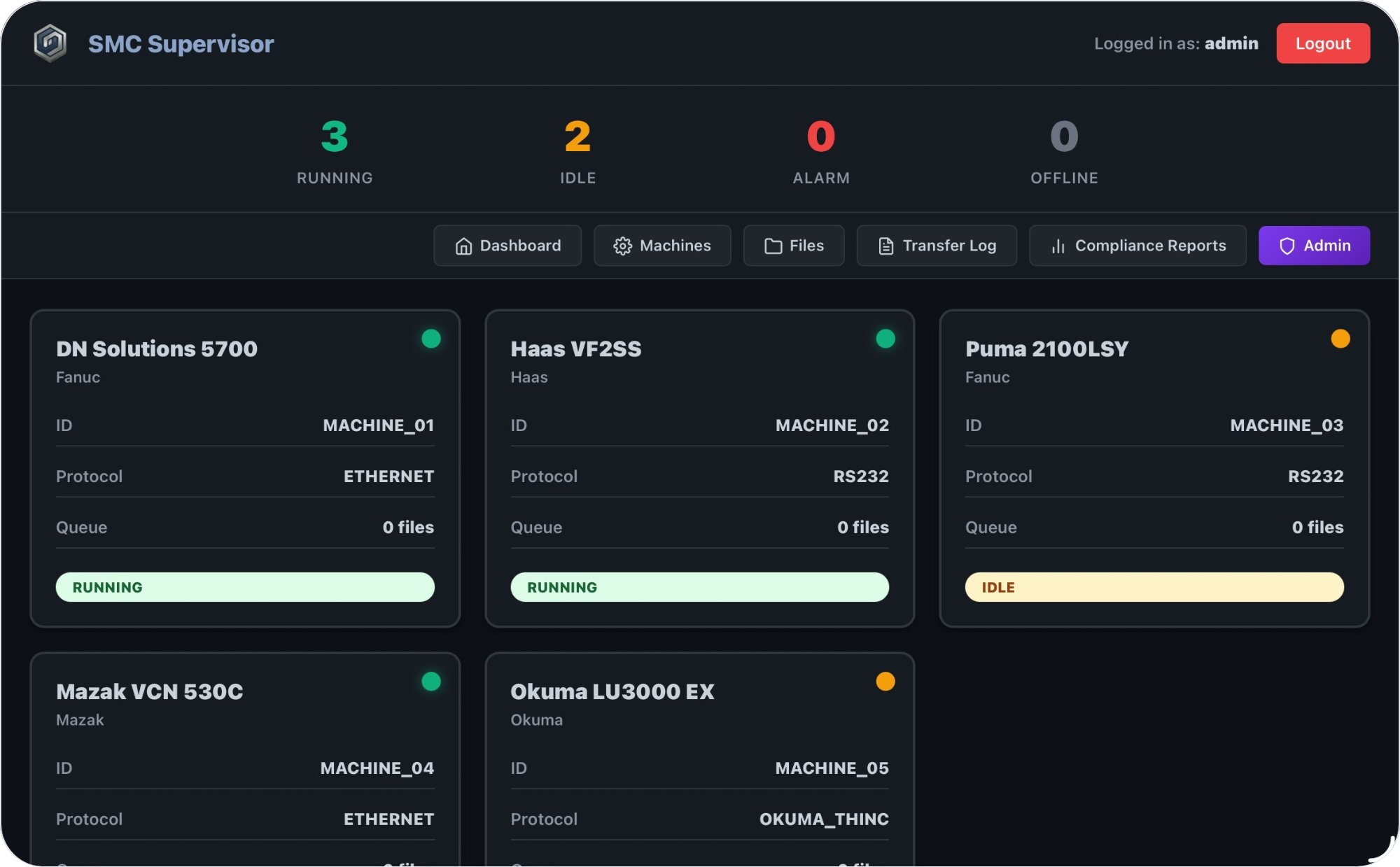
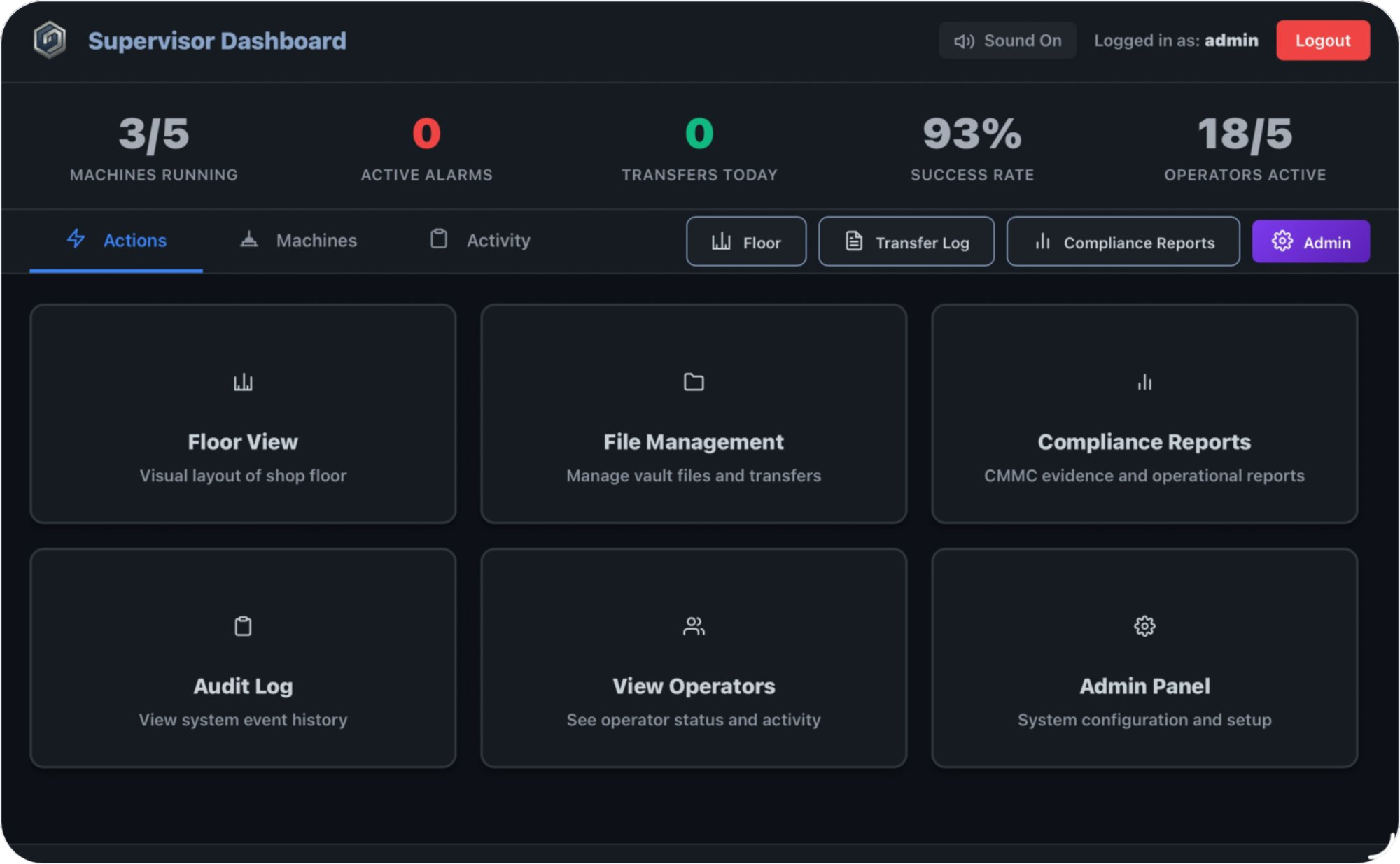
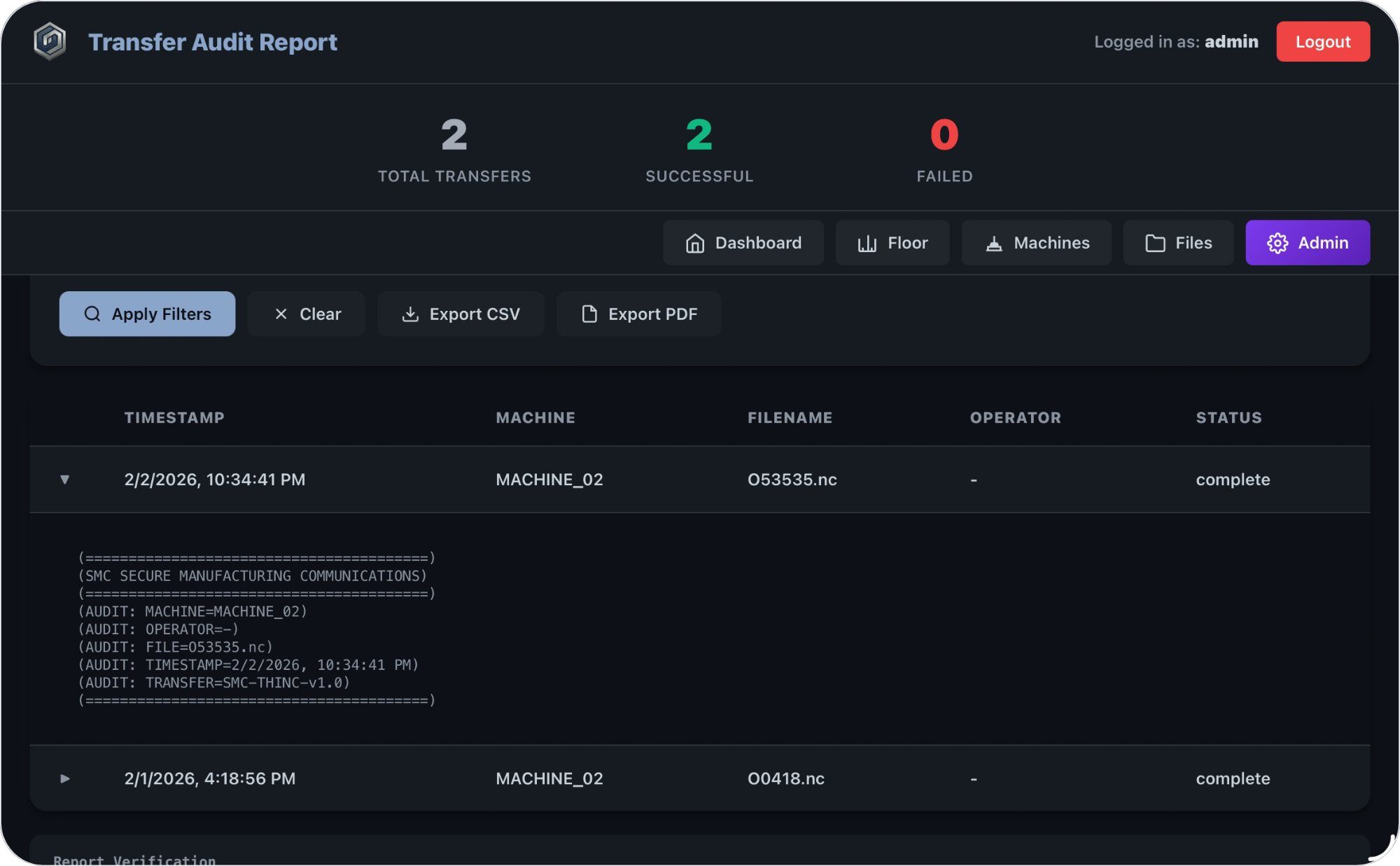
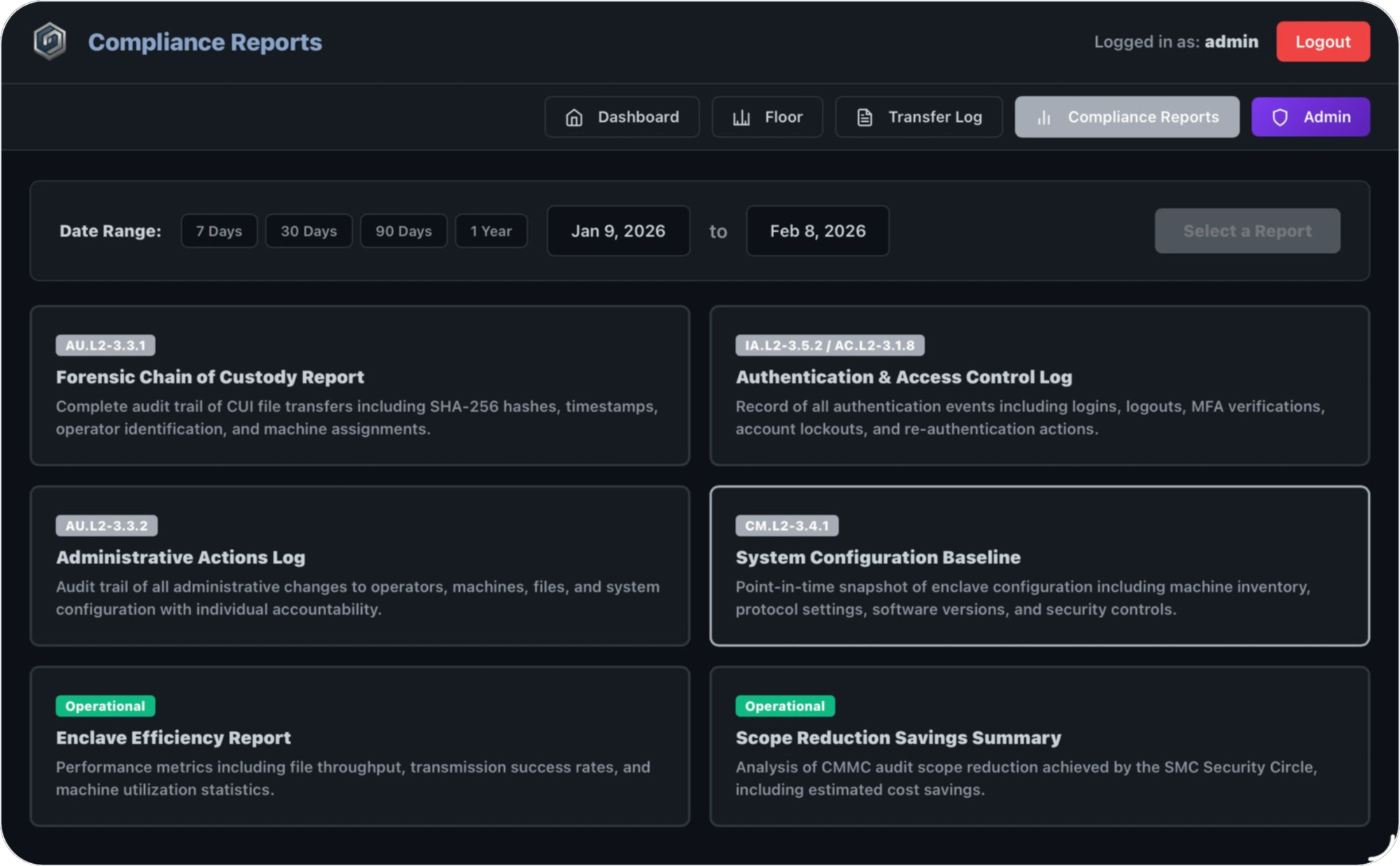
The Secure Manufacturing Cell (SMC) creates a controlled boundary between your CNC environment and your IT network — designed to reduce audit burden, eliminate USB-based transfer risk, and support a more defensible CMMC assessment boundary.